![]()
Charlie Osborne
for Zero Day
| August 9, 2021 — 17:42 GMT (18:42 BST)
| Topic: Security
Our digital selves, more and more, are becoming part of our full identity. The emails we send, the conversations we have over social media — both private and public — as well as photos we share, the videos we watch, and the websites we visit all contribute to our digital personas.
mSpy: Another stalkerware app which markets itself as a service for parents, mSpy for the iPhone allows users to monitor SMS messages, phone calls, GPS locations, apps including Snapchat and WhatsApp, and also includes a keylogger to record every keystroke made on the target device. PhoneSpector: Designed for both Android and iOS handsets, PhoneSpector claims to offer “undetectable remote access.” While a disclaimer says that the service is designed for parents and businesses seeking to track company-owned devices used by employees only, the implementation of the software is made through common tactics used by malware and phishing campaigns. “All you have to do is text or email the OTA (over-the-air) link to the target device and our automated system will set up data transfer protocol and the necessary info for you to monitor the device,” the company proclaims. “Just tap a few buttons, then login to your online account! You can be viewing texts, calls, GPS and more within a few short minutes!”
MobileTracker, FoneMonitor, Spyera, SpyBubble, Spyzie, Android Spy, and Mobistealth are a few more examples of stalkerware which offer similar features, among many, many more in what has become a booming business.
It is also worth noting that you can be tracked by legitimate software which has been abused. Whether or not GPS is turned on, some information recovery apps and services designed to track down a handset in the case of loss or theft can be turned against victims to track their location instead.
What are the the warning signs of spyware?
If you find yourself the recipient of odd or unusual social media messages, text messages, or emails, this may be a warning sign and you should delete them without clicking on any links or downloading any files.
To catch a victim unaware, these messages — known as phishing attempts — will attempt to lure you into clicking a link or executing software which hosts a spyware/stalkerware payload.
Should stalkers employ this tactic, they need you to respond to it. In order to ensure this, messages may contain content designed to induce panic, such as a demand for payment, or they could potentially use spoofed addresses from a contact you trust.
There’s no magic button to send spyware over the air; instead, physical access or the accidental installation of spyware by the victim is necessary.
In the case of potential physical tampering, it can take mere minutes for spyware to be installed on a device. If your mobile or laptop goes missing and reappears with different settings or changes that you do not recognize, or perhaps has been confiscated for a time, this may be an indicator of compromise.
How do I know when I’m being monitored?
Surveillance software is becoming more sophisticated and can be difficult to detect. However, not all forms of spyware and stalkerware are invisible and it is possible to find out if you are being monitored.
Android: A giveaway on an Android device is a setting which allows apps to be downloaded and installed outside of the official Google Play Store.
If enabled, this may indicate tampering and jailbreaking without consent. Not every form of spyware and stalkerware requires a jailbroken device, however. There is an app available in the Play Store called Root Checker that can check for jailbreaking on your behalf.
This setting is found in modern Android builds in Settings > Security > Allow unknown sources. (This varies depending on device and vendor.)
You can also check Apps > Menu > Special Access > Install unknown apps to see if anything appears which you do not recognize, but there is no guarantee that spyware will show up on the list.
Some forms of spyware will also use generic names to avoid detection. If a process or app comes up on the list you are not familiar with, a quick search online may help you ascertain whether it is legitimate.
iOS: iOS devices, unless jailbroken, are generally harder to install with malware. However, the presence of an app called Cydia, which is a package manager that enables users to install software packages on a jailbroken device, may indicate tampering unless you knowingly downloaded the software yourself.
If you think your PC may have been infiltrated, check below:
Windows: On Windows machines, double-checking installed program lists — possible through the start bar — and running processes under “Task Manager” may help you identify suspicious programs.
Mac: On Apple Mac machines, you can do the same by clicking “Launchpad,” “Other,” and “Activity Monitor” to check the status of running programs. You can also reach Activity Monitor quickly through Spotlight.
An antivirus scan is also a recommended way to remove spyware and PUP.
In the cases of Android and iOS devices, you may also experience unexpected battery drain, as well as unexpected or strange behavior from the device operating system or apps — but in the latter case, many users of stalkerware will try not to play their hand.
As with most things in life, trust your instincts. If you think something is wrong, it probably is — and you should take steps to seize control of the situation.
How can I remove spyware from my device?
This is where things get difficult. By design, spyware and stalkerware are hard to detect and can be just as hard to remove. It is not impossible but may take some drastic steps on your part.
When removed, especially in the case of stalkerware, some operators will receive an alert warning them that the victim device is clean. In addition, should the flow of information suddenly cease, this is a clear indicator that the malicious software has been eradicated.
- Run a malware scan: On both mobile and PCs there is a variety of mobile antivirus solutions available which may be able to detect and remove basic forms of spyware. This is the easiest solution available but may not prove effective in every case.Change all of your passwords: If you suspect account compromise, change every password on every important account you have. Many of us have one or two central accounts, such as an email address, which will act as a hub for other accounts and password recovery. Begin there.Enable two-factor authentication (2FA), in which account activity and logins require further consent from a mobile device, can also help protect individual accounts.Consider creating a new email address, known only to you, which becomes tethered to your main accounts.Update your OS: It may seem obvious, but when an operating system releases a new version which often comes with security patches and upgrades, this can — if you’re lucky — cause conflict and problems with spyware. In the same way as antivirus solutions, keep this updated.Protect your device physically: A PIN code, pattern, or enabling biometrics can protect your mobile device from future tampering. If all else fails, factory reset: Performing a factory reset and clean install on the device you believe is compromised may help eradicate some forms of spyware and stalkerware. However, make sure you remember to back up important content first. On Android platforms, this is usually found under Settings > General Management > Reset > Factory Data Reset. On iOS, go to Settings > General > Reset.
Unfortunately, some stalkerware services claim to survive factory resets. So, failing all of that, consider throwing your device in the nearest recycling bin and starting afresh.
Removal of different brands
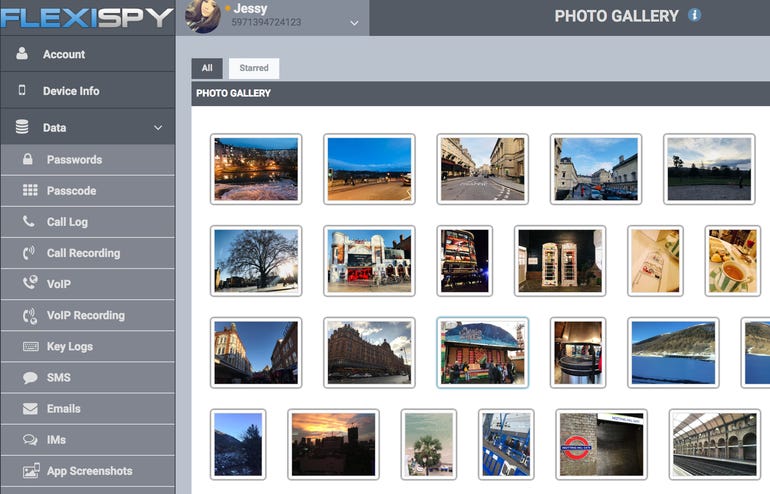
FlexiSpy removal: FlexiSpy may masquerade on Android devices under the name “SyncManager.” If you find this app on your phone, try to uninstall it directly, and then restart your phone. However, it may also appear under another generic name, and so before deleting any apps, perform a search on the app name first.
mSpy: To remove mSpy, instructions are here as long as you have physical access to the device. On the iPhone, you need to access Cydia, search “Installed” and look for “IphoneInternalService.” Press modify and remove. Additional options to try are explained here.
So, what are Google and Apple doing about the problem?
Both Google and Apple are generally quick off the mark if spyware or other forms of malicious apps manage to circumvent the privacy and security barriers imposed for applications hosted in their respective official app stores.
In July 2019, Google removed seven apps from the same Russian developer from the Play Store. While marketed as employee and child trackers, the tech giant took a dim view of their overreaching functions — including GPS device tracking, access to SMS messages, the theft of contact lists, and potentially the exposure of communication taking place in messaging applications.
When it comes to Apple, the iPad and iPhone maker began a crackdown on parental control apps April 2019, citing privacy-invading functions as the reason for some iOS apps to be removed from the App Store. In some cases, Apple requested developers to remove functions, whereas, in others, the apps were simply removed. The company offers its own parental device control service called Screen Time for parents that want to limit their children’s device usage.
Surveillance without consent is unethical and in domestic situations causes a severe imbalance in power. If your sixth sense says something is wrong, listen to it.
A physical object is not worth sacrificing your privacy for. Should your device become compromised, take back control of your right to privacy — whether or not this means replacing your handset entirely.
Security
Kaseya ransomware attack: What you need to know
Surfshark VPN review: It’s cheap, but is it good?
The best browsers for privacy
Cyber security 101: Protect your privacy
The best antivirus software and apps
The best VPNs for business and home use
The best security keys for 2FA
How victims who pay the ransom encourage more attacks (ZDNet YouTube)
Related Topics:
Mobility
Security TV
Data Management
CXO
Data Centers
![]()
Charlie Osborne
for Zero Day
| August 9, 2021 — 17:42 GMT (18:42 BST)
| Topic: Security